Lightweight rogue access point detection algorithm for WiFi-enabled Internet of Things(IoT) devices - ScienceDirect

Client-side rogue access-point detection using a simple walking strategy and round-trip time analysis | EURASIP Journal on Wireless Communications and Networking | Full Text

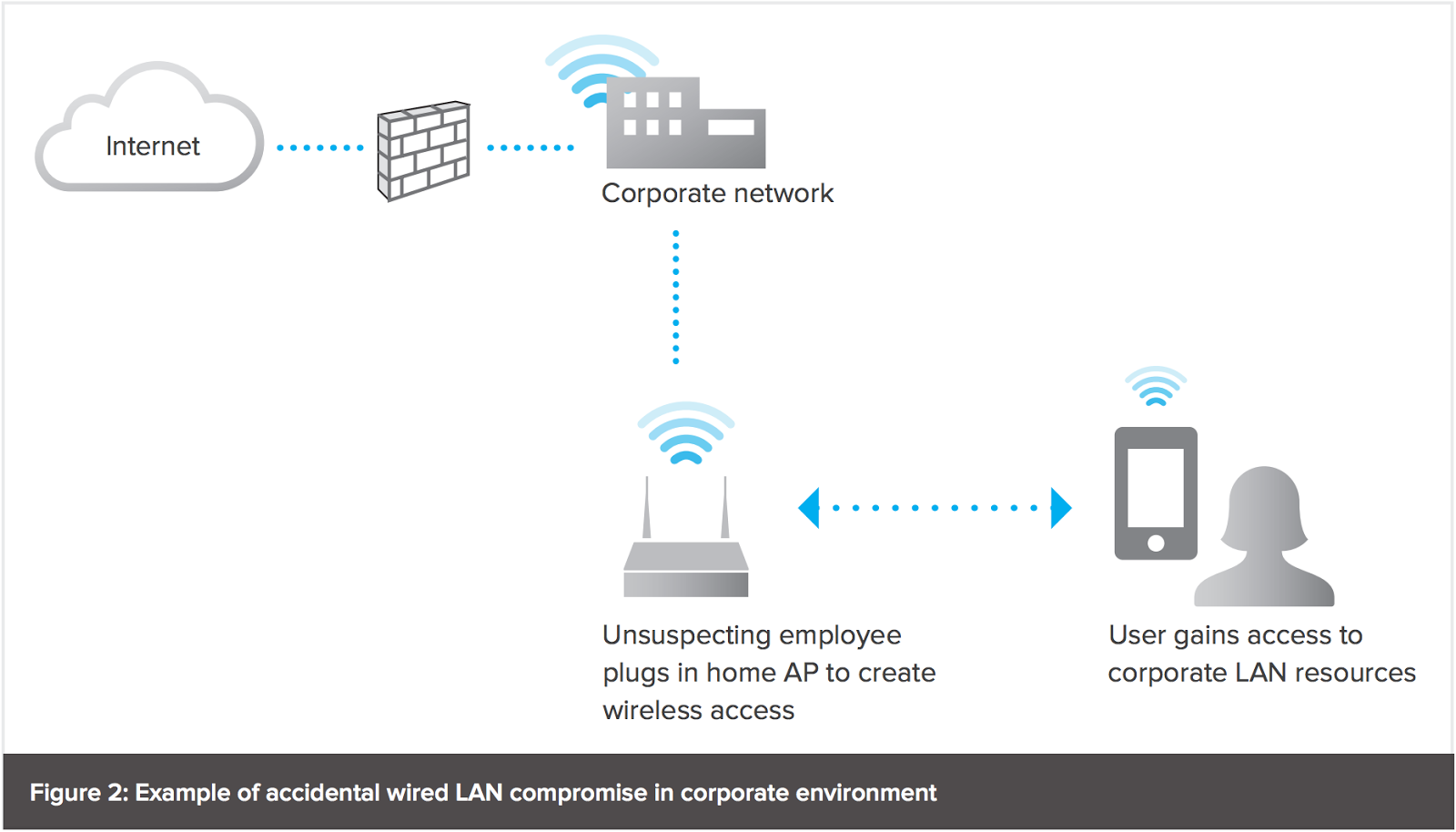
This figure shows the setup of a rogue AP. A rogue AP is connected to... | Download Scientific Diagram
![Unsecured Rogue Access Point Allows Anyone to Connect to the Network [17] | Download Scientific Diagram Unsecured Rogue Access Point Allows Anyone to Connect to the Network [17] | Download Scientific Diagram](https://www.researchgate.net/publication/276230435/figure/fig3/AS:668979894951955@1536508644638/Unsecured-Rogue-Access-Point-Allows-Anyone-to-Connect-to-the-Network-17.jpg)
Unsecured Rogue Access Point Allows Anyone to Connect to the Network [17] | Download Scientific Diagram

Client-side rogue access-point detection using a simple walking strategy and round-trip time analysis | EURASIP Journal on Wireless Communications and Networking | Full Text



![PDF] A Flexible Framework for Rogue Access Point Detection | Semantic Scholar PDF] A Flexible Framework for Rogue Access Point Detection | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/5f7a2fec5198aa5b1f3c846b4db50aec4dff4e3b/29-Figure2.2-1.png)







![PDF] A Review of Online Rogue Access Point Detection | Semantic Scholar PDF] A Review of Online Rogue Access Point Detection | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/d0ed1b76a7acad87e8bb816c84444e4cf6a64b7c/2-Figure1-1.png)