Creating A Positive Customer Experience: The Essential Elements Of End-User Support And Customer Service | Yuri Shwedoff
Controlling Access to Advanced Compute via the Cloud: Options for U.S. Policymakers, Part I | Center for Security and Emerging Technology

The hand, virtual, and end-effector frames' mapping scheme when the... | Download Scientific Diagram

The hand and end-effector frames' mapping scheme when the user controls... | Download Scientific Diagram
INTRODUCTION TO END USER / END USE CONTROLS FOR EXPORTS OF MILITARY-LIST EQUIPMENT (Agreed by the Plenary, 3 July 2014) This doc
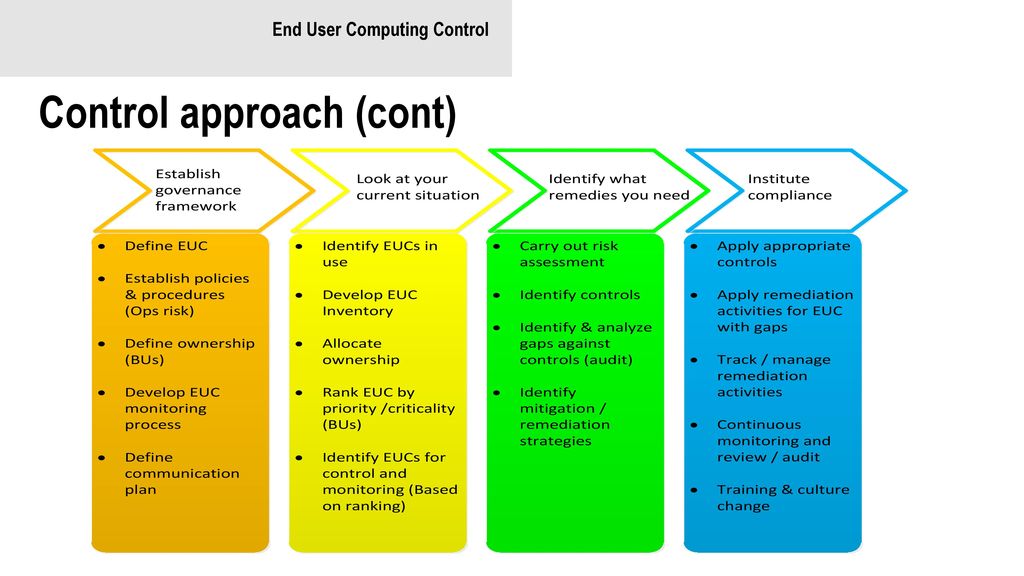
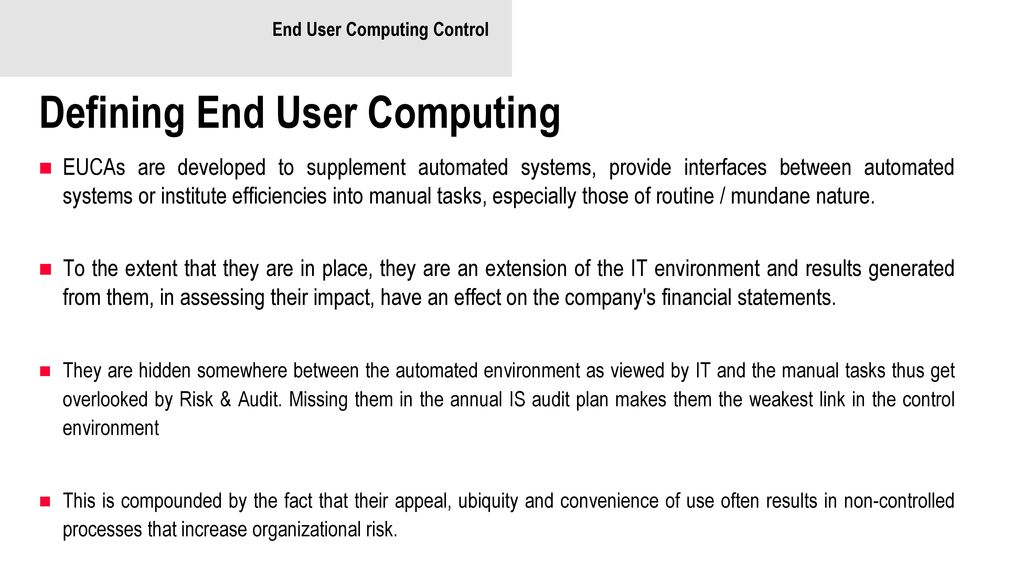
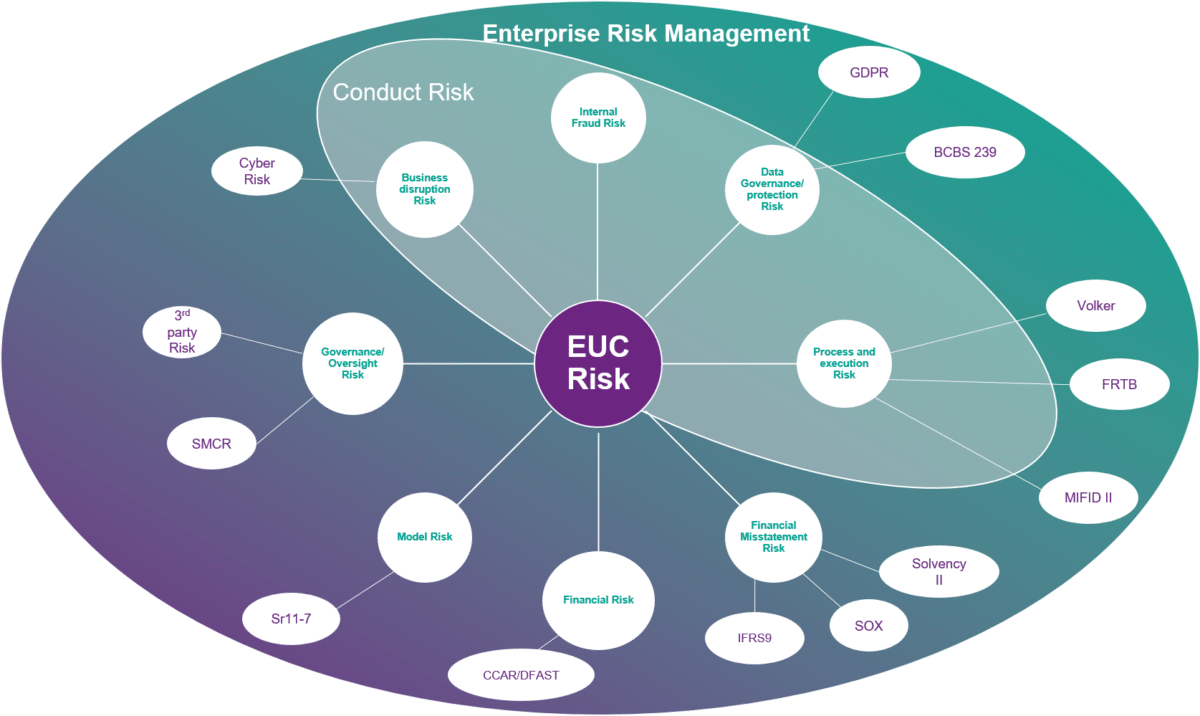
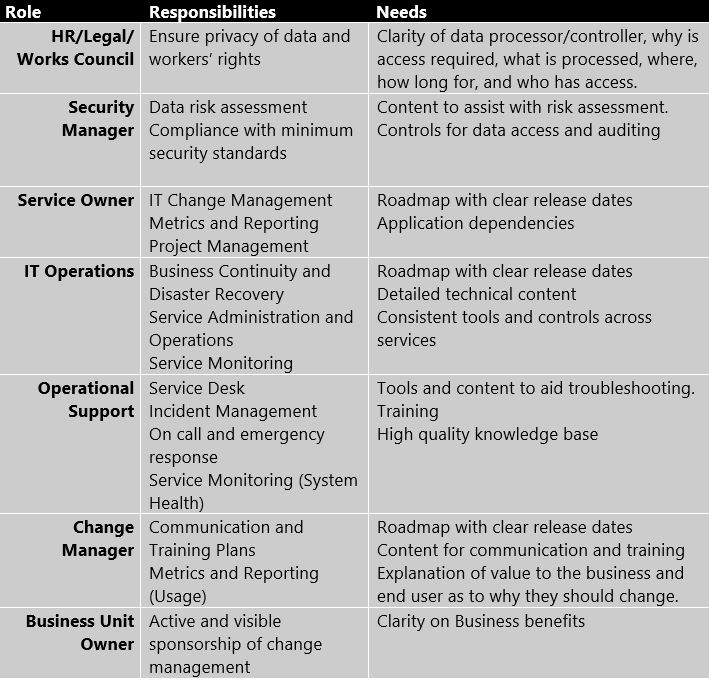
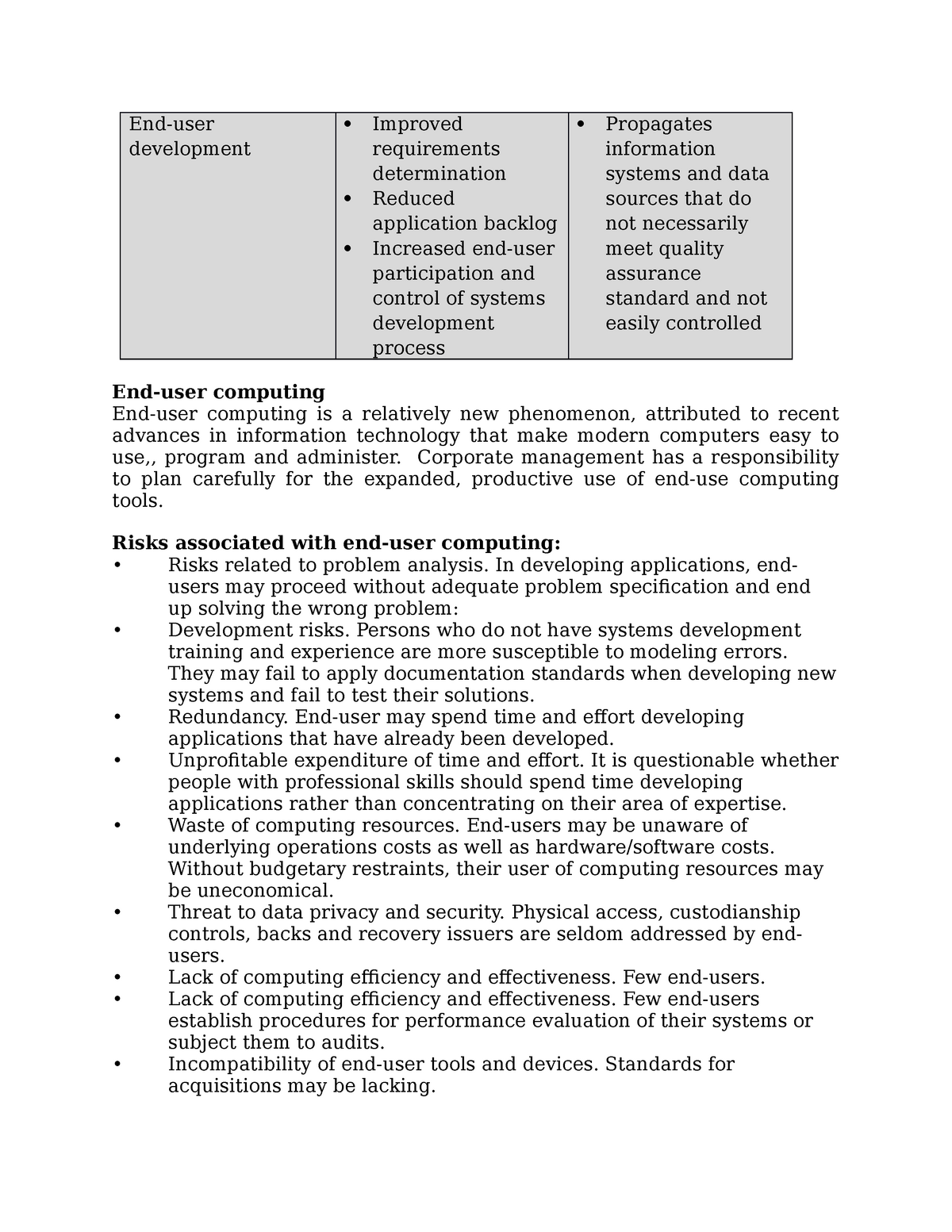
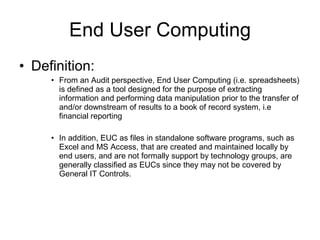
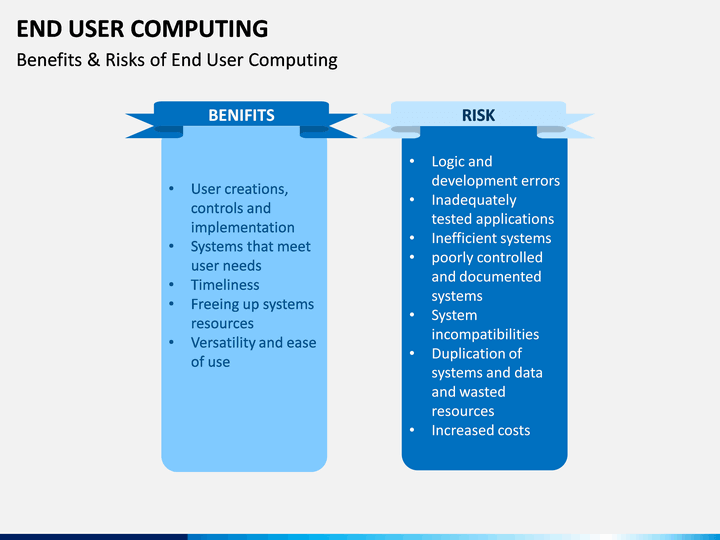
End User Computing IT Essential Components For Complete End User Computing Environment | Presentation Graphics | Presentation PowerPoint Example | Slide Templates